SOC 2 compliance
in one command
Sentrik scans your AI-generated code against 30 SOC 2 Trust Services Criteria rules, blocks non-compliant PRs in CI, and generates audit-ready evidence automatically.
npm install -g sentrik && sentrik scan Free tier includes SOC 2 — no credit card, no time limit.
The SOC 2 Problem
AI writes code faster than your compliance team can review it.
average time to prepare SOC 2 evidence for a single audit
annual cost of enterprise compliance tools like Vanta or Drata
of developers now use AI coding tools (Stack Overflow 2025)
cost of Sentrik's SOC 2 scanning — included in the free tier
30 SOC 2 Rules. Mapped to Trust Services Criteria.
Every finding maps to a specific SOC 2 control. Auditors see the clause, not just a severity label.
CC6 — Logical Access
Hardcoded credentials, missing auth checks, permissive CORS, debug mode in production
CC7 — System Operations
Missing input validation, unsafe deserialization, unparameterized queries
CC8 — Change Management
Dependency pinning, lock file integrity, version control hygiene
CC9 — Risk Mitigation
Error handling, rate limiting, timeout configuration
A1 — Availability
Health checks, graceful shutdown, resource cleanup
C1 — Confidentiality
Encryption at rest, TLS enforcement, secrets in logs, PII exposure
Audit Evidence. Generated Automatically.
When your auditor asks "show me where you implement access controls," you open the Evidence Map.
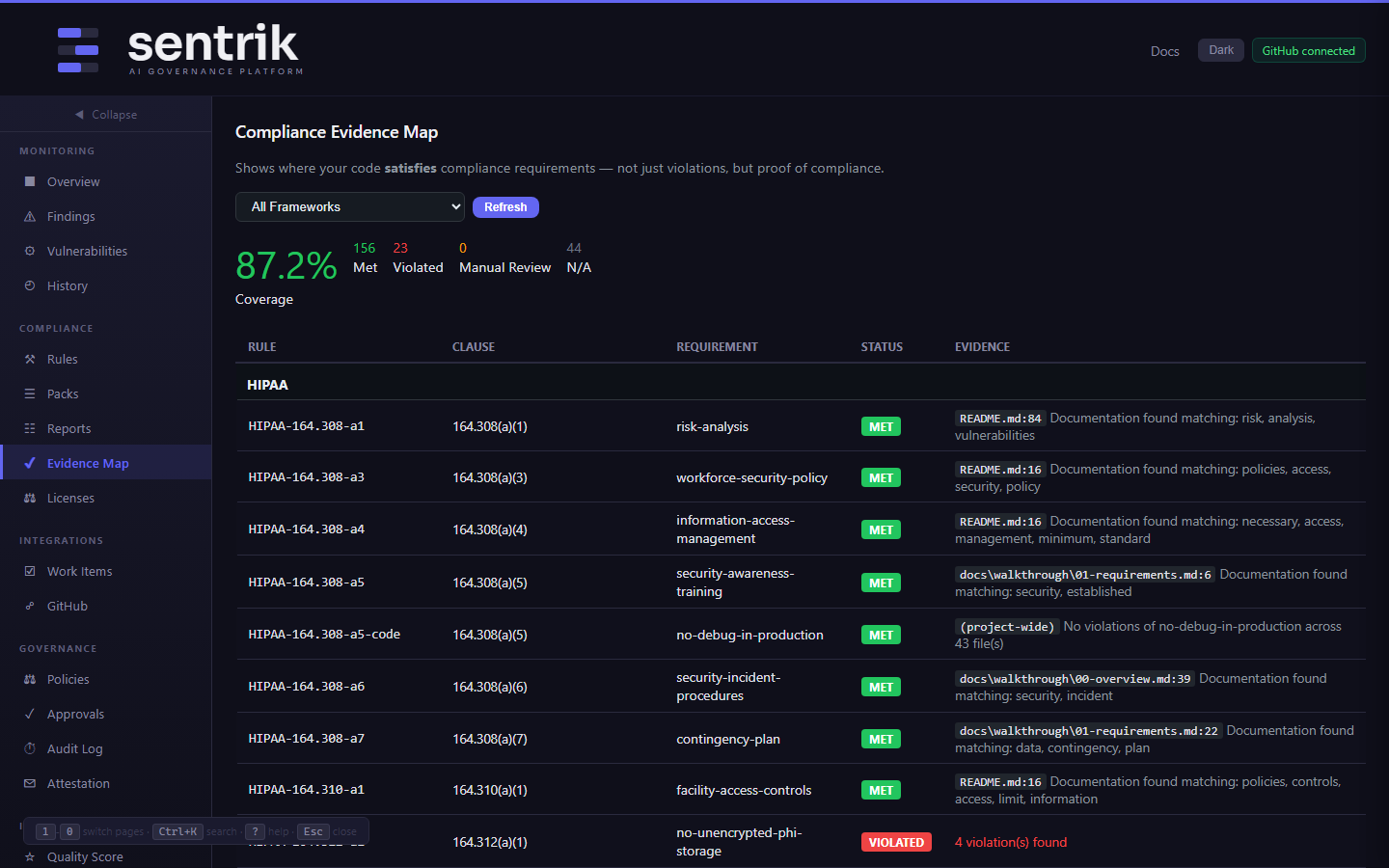
Compliance Evidence Map
Other tools show what's wrong. Sentrik shows what's right. The Evidence Map pinpoints exactly where your code satisfies each SOC 2 control — with file, line number, and matched pattern.
- Per-control status: met, violated, or not applicable
- Coverage percentage across all 30 rules
- Exact code locations as proof of compliance
- Documentation detection in .md, .adoc, .rst files
Three Steps to SOC 2 Compliance
Install
npm install -g sentrik One command. Works on Linux, macOS, and Windows. No configuration needed.
Scan
sentrik scan 30 SOC 2 rules check your code in seconds. Every finding maps to a Trust Services Criteria control.
Ship
sentrik trust-center --org "Your Company" Generate a public trust center page, signed attestation, and audit-ready evidence bundle.
SOC 2 Gate in CI — One Line
# .github/workflows/sentrik.yml
- uses: maxgerhardson/sentrik-community@v1Every PR is checked against SOC 2 controls. Non-compliant code is blocked before it merges.
Start SOC 2 Scanning — Free
SOC 2 is included in the free tier. 30 rules, no credit card, no time limit.
npm install -g sentrik && sentrik scan or