HIPAA compliance
built into CI
Sentrik scans your healthcare code against 25 HIPAA Security Rule controls, detects PHI exposure, enforces encryption requirements, and generates audit evidence for your compliance officer.
npm install -g sentrik && sentrik scan HIPAA pack available on Team tier — $29/month.
The HIPAA Problem
AI agents write healthcare code fast. HIPAA violations ship even faster.
GDPR fines in H1 2025 alone — HIPAA penalties are escalating too
of AI-generated code contains security vulnerabilities
HIPAA Security Rule controls mapped to specific code patterns
to scan your entire codebase for HIPAA violations
25 HIPAA Rules. Mapped to the Security Rule.
Every finding cites the specific HIPAA section. Your compliance officer sees §164.312, not just "high severity."
§164.312(a) — Access Control
Missing authentication, hardcoded credentials, permissive access patterns, debug mode in production
§164.312(a)(2)(iv) — Encryption
Weak cryptography (MD5, SHA-1), missing encryption at rest, plaintext PHI in storage
§164.312(b) — Audit Controls
Missing audit logging in modules handling patient data
§164.312(c) — Integrity
Unsafe deserialization, unvalidated input in healthcare data processing
§164.312(e) — Transmission
PHI in console logs, unencrypted cookies, localStorage with health data
§164.308 — Administrative
Risk analysis documentation, security training records, incident response plans, contingency planning
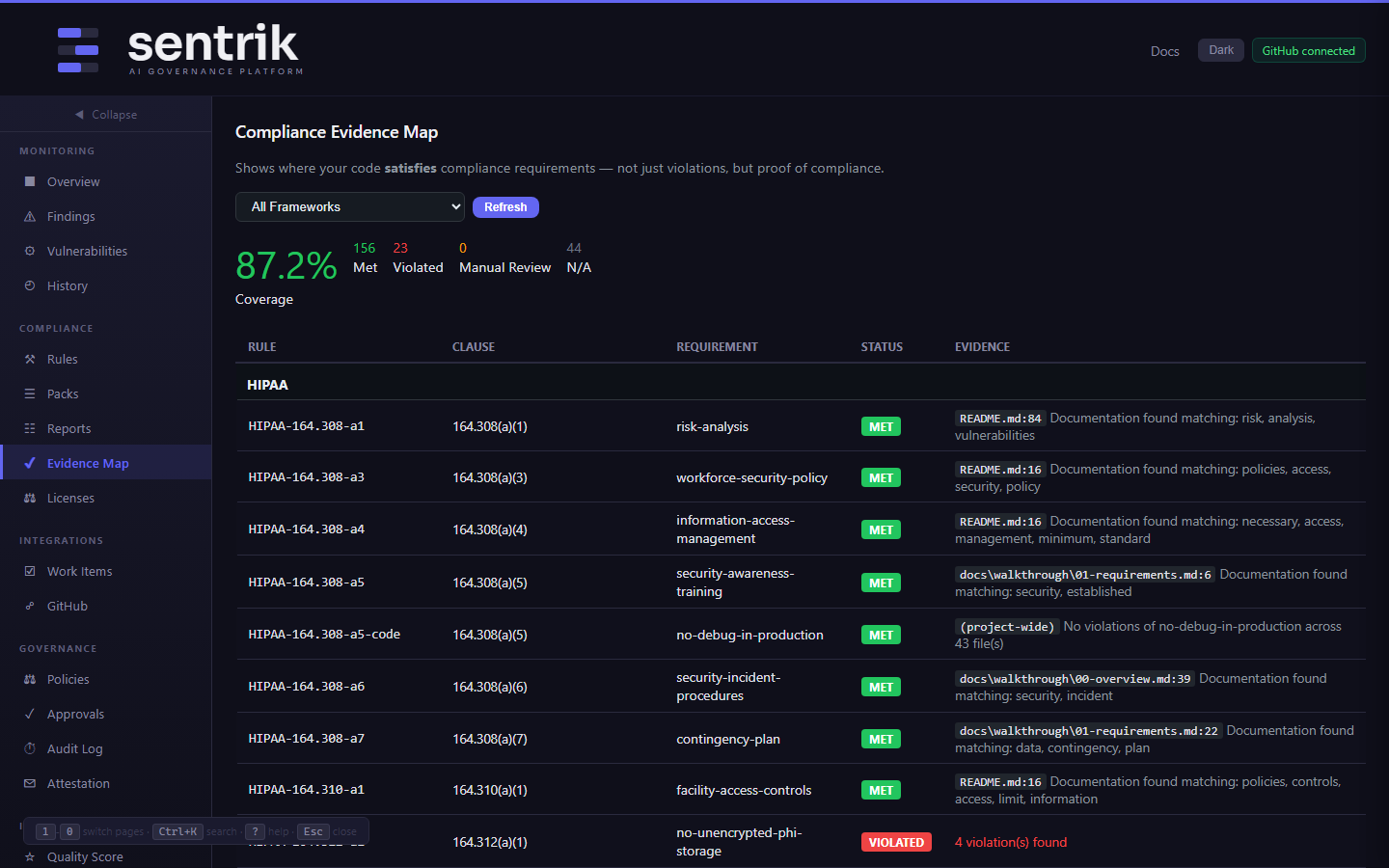
Prove HIPAA Compliance to Your Auditor
The Evidence Map shows exactly where your code satisfies each HIPAA requirement.
Evidence Map for HIPAA
When your auditor asks "show me where you implement audit logging for ePHI access," you open the Evidence Map. It shows:
- §164.312(b) — audit logging found in
middleware/audit.py:14 - §164.312(a)(2)(iv) — AES-256 encryption in
services/encryption.py:45 - §164.308(a)(1) — risk analysis documented in
docs/risk-analysis.adoc
Not just violations — proof of compliance.
PHI Detection Built In
Sentrik detects Protected Health Information exposure before it ships.
PHI in Logs
Detects patient data being written to console.log, print statements, or logging frameworks
PHI in Client Storage
Flags health data stored in localStorage, sessionStorage, or unencrypted cookies
Secrets Detection
Finds hardcoded API keys, database passwords, and tokens that could expose ePHI
Start HIPAA Scanning
25 HIPAA rules on the Team tier. Try the free tier first — includes OWASP and SOC 2.
npm install -g sentrik && sentrik scan or